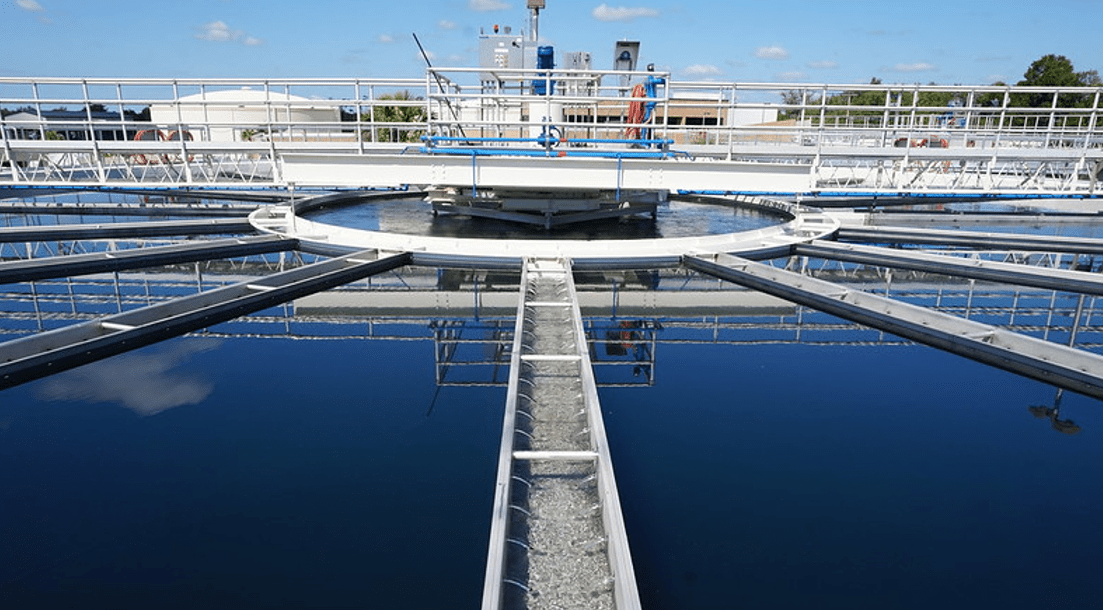
A hacker allegedly tried to poison water that was being processed at a San Francisco Bay Area water treatment plant, according to an NBC News report late last week.
The attack took place on January 15 and involved the person gaining access to the water treatment plant’s network by using a former employee’s TeamViewer account credentials. Having gained access to the plant, the person eliminated the programs that the water plant uses to treat drinking water.
According to a confidential report compiled by the Northern California Regional Intelligence Center and seen by NBC, the hack wasn’t discovered until the next day.Subsequently, the installation changed their passwords and reinstalled the programs.”No failures were reported as a result of this incident and no one in the city reported suffering from any water-related failure illness,” the report said.
Michael Sena, NCRIC’s executive director, denied the report.”No one tried to poison our water.That’s not accurate,” Sena told the San Franciso Chronicle, noting that manipulation of computer programs is unlikely to result in poisoning.
“It takes a lot to influence a water supply chain,” Sena explained.”For a big impact, there has to be a big change in the chemicals in the system.The amount of chemicals it would take to cause harm to people….The numbers are astronomical.
“The threat to the Bay Area’s water supply isn’t a treatment plant’s first commitment and probably won’t be the last. In February, an unknown attacker accessed a water treatment plant in Oldsmar, Florida, and attempted to poison the water supply by increasing the flow of sodium hydroxide to toxic levels.In that case, the attacker was detected before the water supply could be affected.
“While it’s important to be on the lookout for important events, we should also avoid sensational headlines meant to spread fear,” Chris Grove, a technology evangelist at Nozomi Networks Inc., a specialist in critical infrastructure security, told SiliconANGLE. “Some headlines are taking the action of erasing the code and jumping into the attempted mass poisoning. There was no attempt to poison the water supply.”
That said, he added, “this is a stark reminder of how unsafe our nation’s water facilities are.”Grove noted that the case highlights the lack of two-factor authentication, password procedures, monitoring and other defenses.”There are a lot of facilities that are in the same situation: the same remote access issues, the same password issues, and the same underfunded and understaffed cybersecurity advocates,” he said.
James Carder, chief security officer, security intelligence firm LogRhythm Inc., said the incident is a prime example of how cyber attacks on critical infrastructure can harm the physical security of citizens and are only growing.
“Over the past 20 years, industrial control systems have largely neglected operational technology and operational risk by separating data to compensate for deficiencies in network security and the physical isolation of insecure network platforms,” Carder explained.”This means that critical infrastructure operations are full of opportunities for bad actors to target and remove their systems.”
Source: Link


Get Involved & Participate!
Comments