We have already talked about the need to perform an industrial cyber risk analysis, and this time we will address one of the mistakes most commonly assumed “and accepted” by enthusiasts in industrial cybersecurity. Risk analysis based on vulnerabilities or consequences? To address this analysis we must first remember how industrial cybernetic risk should be calculated and evaluated from its mathematical expression: R = A x V x C (Ref. ISA/IEC-62443) From the equation it follows that the increase or decrease in risk will be proportional to the increase or decrease of the factors involved in multiplication. Whichever of its variables is 0, the risk will be 0. Let’s analyze each factor and the possibility of making it tend to zero. Many find it very difficult to understand the equation, stare at it, and fail to fully understand it. But there’s also the vulnerability, others say. Understanding the risk equation requires a thorough understanding of how to use it, and this requires practical experience. It is not enough to know how to do mathematical accounts, nor to study by heart all the definitions of the ISA/IEC-62443. In essence, the equation is irrelevant if you do not know how to apply it in practice.
The Threats
Threats can be internal, external, unintentional, intentional, with different levels of motivation and resources. They can be natural, originated in people and / or technological. Some threats can be controlled and reduced, while others we can do nothing to control them, since they do not depend on us (the owners of industrial plants). We’ll leave the Threats for another time. While they are part of the equation and an important part of the methodology, we will talk more about the threats in another post.
Vulnerabilities
Let’s start with vulnerabilities by asking ourselves the following question:
- Is it possible to set the vulnerabilities involved in an industrial process to zero, if new vulnerabilities appear every day?
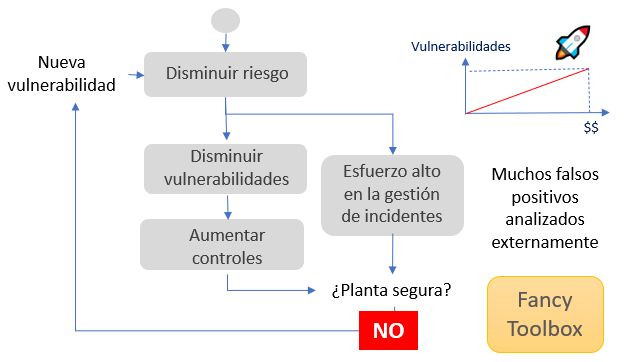
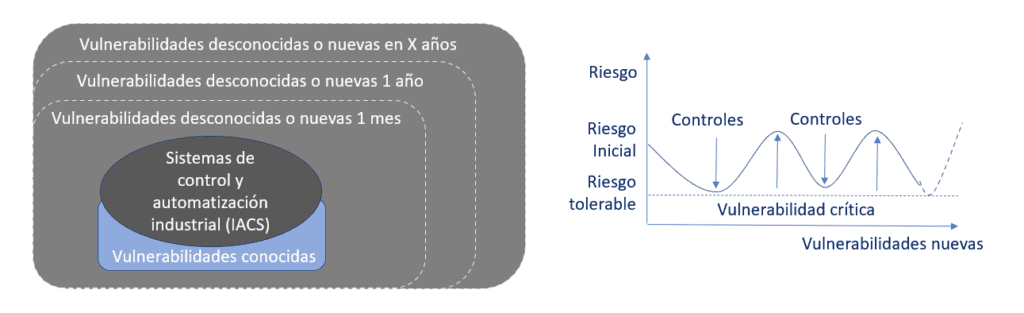
Vulnerabilities can be controlled if they are known. This is possible through gap analysis based on good practices and analysis of technological vulnerabilities of cyber components. We must bear in mind that vulnerabilities are changing and increase over time, there are vulnerabilities that are not yet known and there are people dedicated to discovering new ones, both for better and for worse. It usually happens that some recently “discovered” or rather recently published were there for many years. If we analyze the risk based on the vulnerabilities and put them in a graph as a function of time, we can show that, although the necessary controls are implemented and mitigated, the fact of having new vulnerabilities makes it a new risk or danger that will have to be mitigated again, that is, another expense. This will be a constant effort to prevent cyber incidents from occurring.
Here comes a very important question to ponder. If I don’t know of the existence of a vulnerability, does it mean that someone else can know, does it mean that there is no risk?
This variable behavior of vulnerabilities leaves probability to change, and therefore the risk increases and decreases at the same rate. This approach consists of a short-term risk mitigation strategy. As short as the time it takes to know a new vulnerability, which today is almost the same as nothingness. In the field of industrial safety, this approach is neither effective nor efficient in protecting risk recipients from constant danger.
It is a frequent practice inherited from information security to classify the severity of a vulnerability, making use of a valuation system (scoring).
Many vendors employ various vulnerability-based methods to calculate risk in industrial systems. What happens if it is suddenly discovered that our PLC has 3 new vulnerabilities classified as critical or very critical? The risk would be “suddenly” very high, right? Then… if so… Should we “immediately” start evacuating the plant? Certainly not! With approaches based on vulnerability assessment, we will be questioning the digital infrastructure of the plant all the time, we would even be constantly questioning the decisions that have been made, recently.
When the aim is to protect people’s lives, the environment and industrial equipment, these methods are not suitable, even if they are short-term. We must employ methods and mechanisms for the mitigation of risks that are long-term, that convey calm, security and confidence in the industrial technological infrastructure.
The obsession with the study of vulnerabilities is a preferred approach for lovers and experts in information security because in essence they are protecting data and information. It’s what they know how to do, it’s what they’ve done all their lives. They seek to prevent incidents from occurring, protecting cyber assets.
Here is one of the most significant mistakes that the vast majority of the information security community makes when dealing with industrial systems. These start from an incorrect working hypothesis, assuming that “by avoiding the cyber incident they are protecting people’s lives, the environment and other risk recipients.” Which is false, and far removed from reality!
It is very important to emphasize that when looking at the risk from the point of view of vulnerabilities, in this case the company is limited to analyzing the IACS, losing the physical dimension, when these in themselves do not represent a real danger to the plant. A basic example of this is when a PLC is affected by a threat and stops working, this fact in itself is not relevant, what is relevant is the industrial process that is being controlled, for this reason analyzing the vulnerabilities of the PLC and mitigating them does not mean that it is contributing to the real mitigation of risk.
No matter how much is spent or invested, any information security approach applied on industrial systems to protect the industrial plant will be insufficient. You can help, but it will always be insufficient.
Others prefer to use methods of statistical calculations, based on information accumulated about a recent past, which are also wrong and do not serve the field of industrial safety, but we will leave this for another publication.
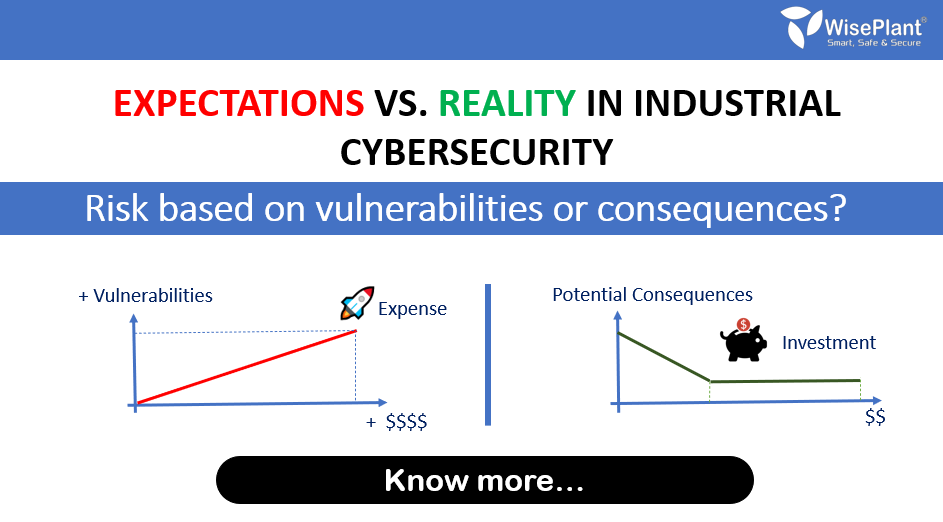
Information security methods and techniques have been generating many expectations and promises, but the sad reality is that they are insufficient. Even worse is that they require a larger budget, and a greater constant expense. And the risk remains unmitigated!
The Consequences
Now let’s continue with the analysis of the consequences and their impact by answering the following question:
- Is it possible to prevent consequences of occurring even though at some point or circumstance the cyber components are compromised?
The answer to this question is very important. Anyone who does not know this answer does not understand ISA/IEC-62443-3-2, nor the essence of industrial cyber risk mitigation by design. The answer to this very important question is “YES”, you can! In fact, it is what makes ISA/IEC-62443 a unique standard. Some might go so far as to say that this is the heart of ISA/IEC-62443.
This is why the correct application of the risk equation requires a methodology and a very good understanding of the concepts. Practical experience is required (it is essential) and being very familiar with RAGAGEP (Recognized And Globally Accepted Good Engineering Practices) requirements and forms of industrial risk treatment.
This is what we teach in the ISA IC33 and WisePlant 2160 courses. The problem is that “if these concepts are not put into practice quickly most people end up forgetting or misinterpreting them.” They require hands-on experience. It’s very simple, put another way: “You can’t learn to ride a bike if you don’t get on it.”
In the field of industrial cybersecurity we are protecting life, the environment, industrial equipment, among others. Those who view industrial risk as a mere economic impact are also not well oriented, unfortunately, they still do not understand the industrial environment on which they are working.
Here comes the substantial difference that industrial cybersecurity has with respect to information security. While information security experts seek to prevent cyber incidents (even though they fail to do so), industrial cybersecurity experts seek to prevent the consequences for occurring.
Unacceptable consequences are what we must mitigate and prevent from occurring, and even if systems are compromised. The mitigation of industrial cyber risk based on consequences or also called “knowledge-based” must be supported by correct decisions that allow influencing the design or redesign of both the systems and the plant (as one) respecting the laws of physics, chemistry, etc.
Without becoming an exhaustive list, some of the qualities that must be incorporated during the risk assessment process are:
- Detailed knowledge of the SuC (System under Consideration) i.e. of all components of the IACS, including all those that do not have a network connection.
- Develop a knowledge about the industrial process and the consequences that may occur, affecting all potential risk recipients and how they occur.
- Evaluate the effectiveness and efficiency of existing countermeasures (and controls).
- Decide on changes, actions, countermeasures and compensatory controls that are effective, efficient and sufficient to mitigate industrial cyber risks (Consequences).
- It requires a multidisciplinary work where those responsible for the industrial process and the control system, including operation and maintenance, participate.
- Design and implementation of the recommendations resulting from this analysis to mitigate the consequences by making responsible and long-term decisions.
This list lists only what is essential as a starting point for risk analysis based on consequences if we want to achieve the mitigation of all the consequences that are unacceptable, bearing in mind the impact that these can cause to the risk recipients. 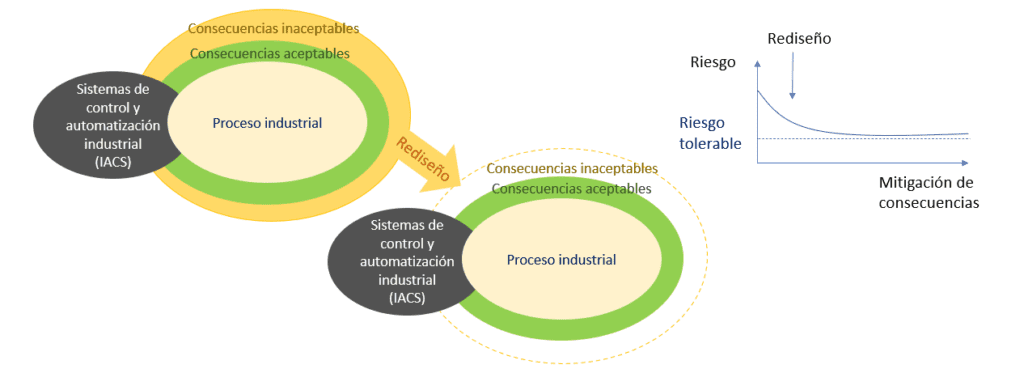
On the consequences there are many issues to mention because most of the professionals in charge of industrial cybersecurity misunderstand the purpose of industrial cybersecurity, which is mainly to protect risk recipients from the consequences that the industrial process can generate in the face of cybernetic affectation to industrial control and automation systems (IACS).
So they mistakenly focus their attention on the IACS and neglect the possible consequences that the industrial process can cause in the physical world.
Now, after contextualizing the implications of a vulnerability-based risk analysis and a consequence-based risk analysis, the following table summarizes the main differences.
Conclusions
Risk management based on vulnerabilities consists of the implementation of generic, complex, short-term solutions, very expensive, being insufficient, causing a very high dependence on controls, monitoring, and distant analysis of cyber incidents.
- Current situation: preferred by most.
- Results: insufficient, expensive, short term.
Consequence-based risk management consists of developing a long-term solution at a lower cost, where the decisions made are the result of deep knowledge, influencing the design of the system and the plant at the same time with local capacity and immediate action.
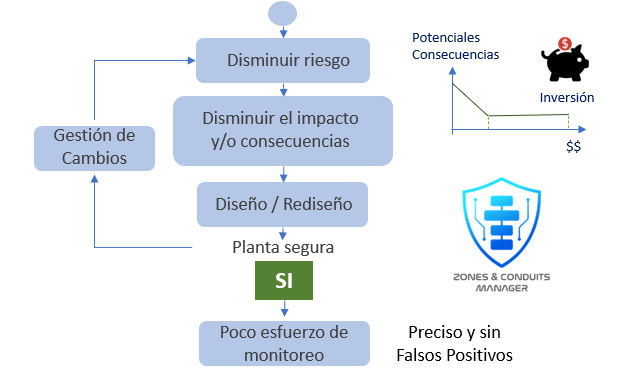
- Current situation: ZCM System and WBS Methodology
- Results achieved: effective, efficient, sufficient.





Get Involved & Participate!
Comments